Restrictions
Important limitations and assumptions of the plugin:
- Installation of the plugin requires Administrator permissions to run the deployment scripts from the SharePoint Management Shell (PowerShell).
- While a single installation of the plugin's .wsp file is necessary, a separate execution of the model deployment script is needed for each different Content Source that is published into StageR.
- SharePoint enforces a 2min timeout when it does the initial request of the ids of the items to crawl. This limits the size of the crawl to what the performance of the StageR server, MongoDB database and network latency can allow. So far the maximum number of items per crawl has stabilized around 100000.
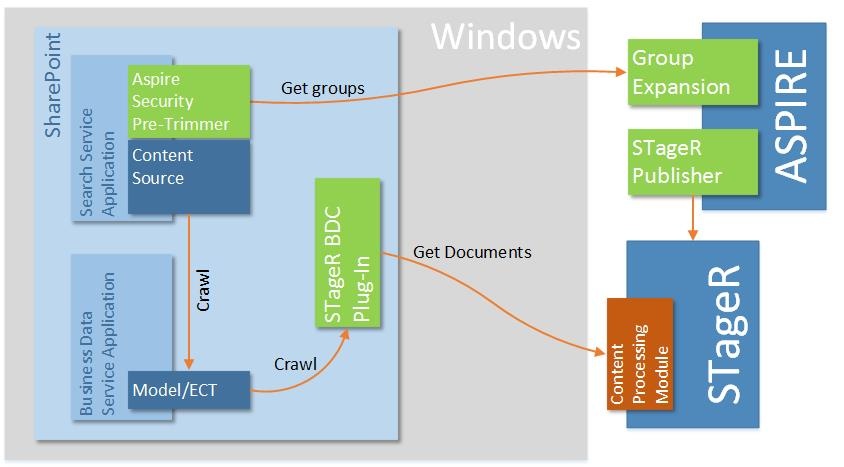
Architecture
SharePoint Components
StagerBDCPlugin
The plugin is deployed as a .wsp file that SharePoint installs as a global farm solution. It implements the SharePoint BDC standard for custom connectors and gets executed from a SharePoint content source. In version 2.X this file contains only the necessary logic to instance the business components through Reflection.
BDCBusinessLogic
The business logic is also deployed as a .wsp file. It contains the necessary components to extract the contents from STageR and hand them to SharePoint for indexing.
Security Trimming
Security trimming is available within SharePoint itself. To make this work, a SecurityTrimmerPre interface must be created (see SharePoint Security Pre-Trimmer 3.2).
The ISecurityTrimmerPre interface adds "claims" to the query prior to actually executing the search query. With the exception of deny ACLs, the function of the ISecurityTrimmerPre module is to always add results to the result set, rather than to remove them. In this sense, it is the opposite of a security trimmer.
It is critical to understand that if the ISecurityTrimmerPre interface malfunctions, then you get no secure search results. (If it performed "classic" security trimming and malfunctioned, then you would get back extra unauthorized results). On each search request, the Security Pre-Trimmer is invoked to enhance the search query with ACL information. This information is retrieved from an Aspire Group Expander (LDAP, Lotus Notes ...)